靶机地址:https://thehackerslabs.com/accounting/
第一次玩TheHackerLabs的靶机,还是先继续win系统的。
Tips: mssql基本操作、NTFS数据流
作者归档:站长
发表评论
HackTheBox Certified Walkthrough
忍着龟速,跟着论坛提示,完成了HTB的Certified,发现DAC还是非常有意思的,瞬间觉得需要恶补域渗透方面的知识。

这是我写的比较详细的一篇Walkthrough,既是自己学习过程的记录,也可供刚刚接触这方面的朋友参考。
HackTheBox Cicada Walkthrough
HackMyVm Wave Walkthrough
靶机下载地址https://hackmyvm.eu/machines/machine.php?vm=Wave。
Tips: shell加解密、常见php扩展名、端口转发、less命令的使用。
整体玩下来还是挺有趣的。
使用dmenu或fzf实现快捷键在tmux当前面板中输入自定义常用指令
在玩靶场的过程中,经常遇到输入一些常见指令的情况,比如nc监听、python切换交互终端等。每次复制粘贴比较繁琐,zsh虽然有历史命令功能,但有时需要配合Ctrl+R进行查找。今天找到了一种更简单的方法,使用dmenu或fzf实现在当前激活的tmux分屏面板中快捷执行保存的常用指令。
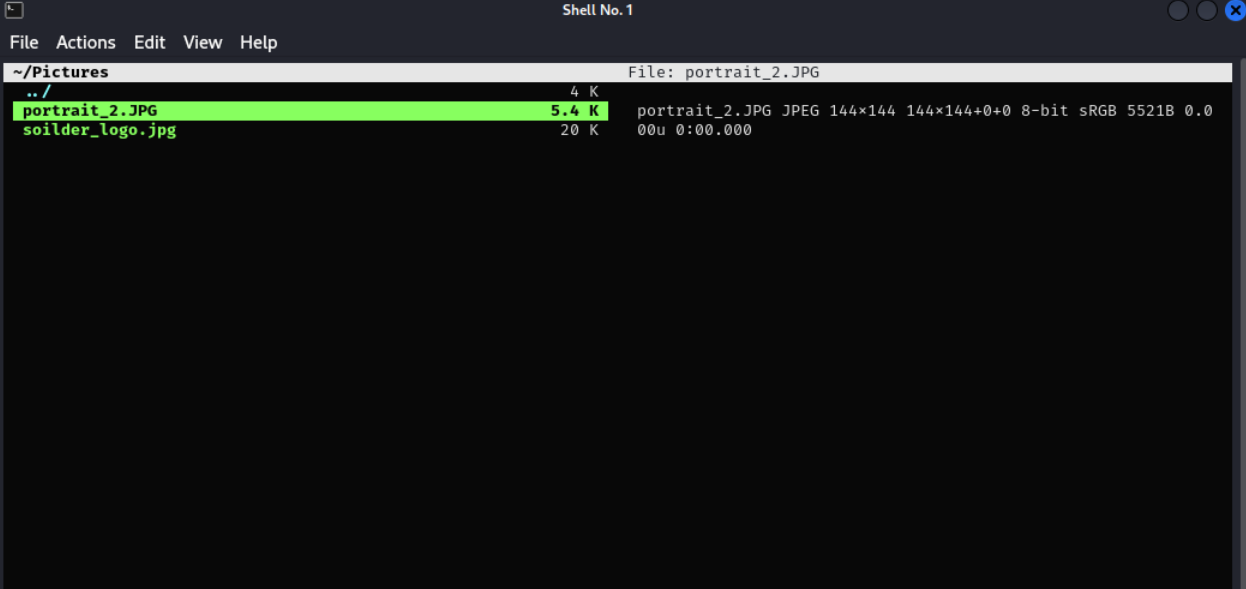
配置vifm,实现命令行中预览图片,回车调用自定义工具查看
VulNyx Hosting Walkthrough
另一台win系统的靶机,下载地址为https://vulnyx.com/file/Hosting.php。
Tips:smb、rpcclient、HKLM备份导出、一些常用的windows命令行。